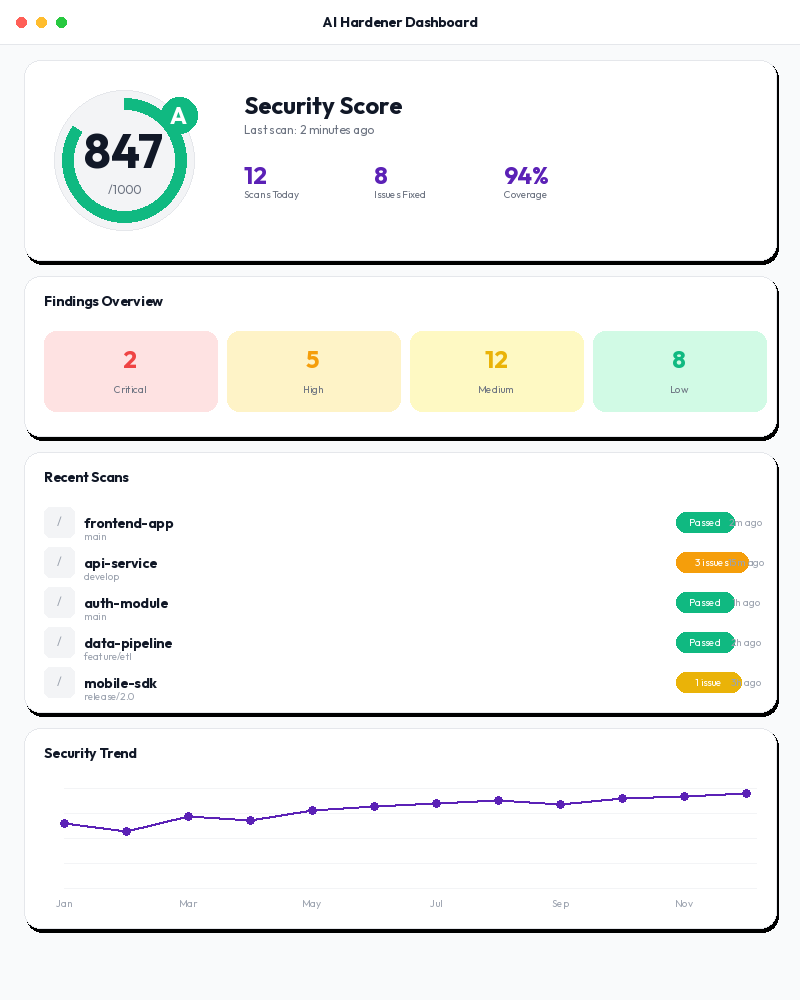
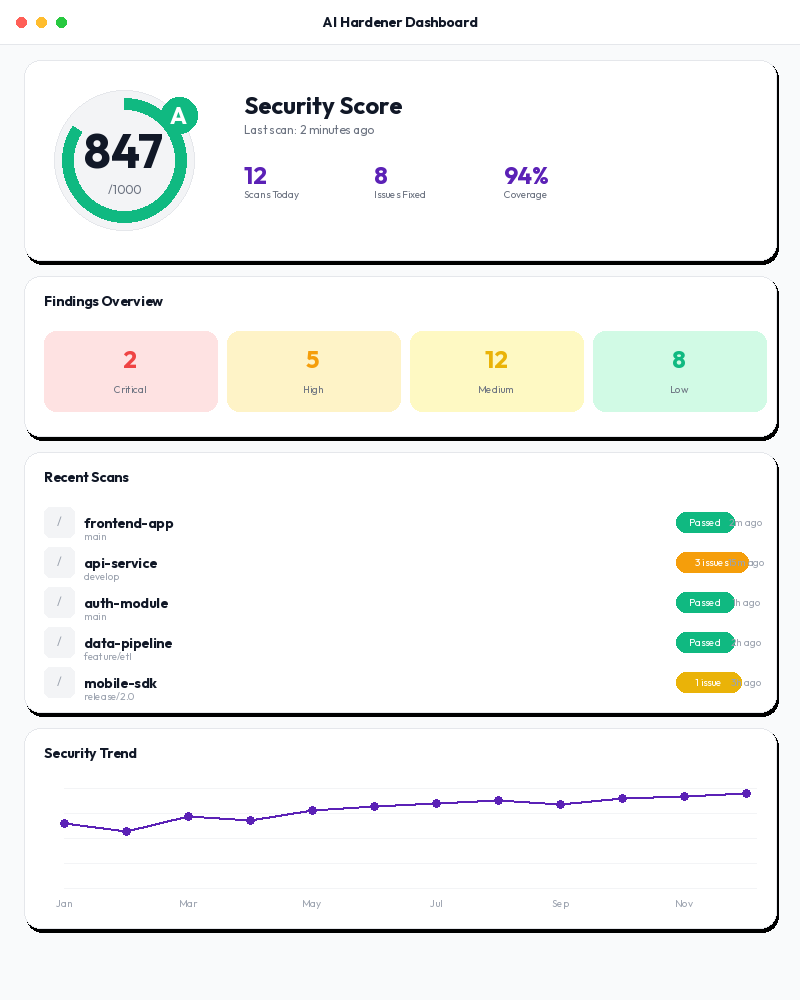
Harden Your Code
Security assurance for AI-first developers. Scan AI-generated code for vulnerabilities, secrets, and misconfigurations — fixing issues before they reach production.
Security assurance for AI-first developers. Scan AI-generated code for vulnerabilities, secrets, and misconfigurations — fixing issues before they reach production.
Powered by 30 open-source security scanners
Every AI-generated feature ships potential vulnerabilities. Without automated security scanning, critical issues reach production undetected.
AI-generated code routinely introduces injection vulnerabilities that traditional code review misses.
API keys, tokens, and credentials embedded directly in source code by AI assistants and developers alike.
Outdated libraries with known CVEs pulled in automatically. Container images with critical vulnerabilities.
Terraform, CloudFormation, and Kubernetes manifests with overly permissive access and exposed ports.
Comprehensive code security covering SAST, DAST, SCA, secrets, containers, IaC, API testing, load testing, and supply chain verification.
Static and dynamic analysis across 15+ languages. Semgrep, Bandit, Gosec, ESLint Security, PMD, Nuclei, and OWASP ZAP.
Gitleaks and detect-secrets catch API keys, tokens, passwords, and credentials before they reach your repository.
Trivy, Grype, pip-audit, and Dockle scan dependencies, container images, and package manifests for known CVEs.
Checkov scans Terraform, CloudFormation, Kubernetes, Helm, and Dockerfile configurations for security misconfigurations.
Newman, Pact, RESTler for API contract testing. Locust, Artillery, K6 for performance and load testing under stress.
Syft generates SBOMs. Cosign verifies signatures. in-toto provides provenance attestation. OPA enforces policies.
From connection to security report in under 60 seconds.
Point Code Hardener at your repository, container registry, or running application. Works with any language or framework.
$ curl -X POST /api/v1/scans \
-d '{"target": "/path/to/repo",
"profile": "standard"}'30 specialized scanners run in parallel. Language auto-detection selects the right tools. Quick scans finish in under 60 seconds.
Plain-language findings mapped to CWE and OWASP. Actionable remediation guidance with fix suggestions and severity scoring.
All permissively licensed (Apache 2.0, MIT, BSD). Zero vendor lock-in.
SAST (multi-lang)
SAST (Python)
SAST (Go)
SAST (JS/TS)
SAST (Java)
DAST scanner
DAST proxy
SCA + containers
SCA vulnerabilities
Python SCA
Container linting
Secret detection
Secret baseline
IaC scanning
API collections
Contract testing
API fuzzing
Load testing
Load testing
Performance
Browser testing
Visual regression
Accessibility
SBOM generation
Signature verify
Provenance
Policy engine
Config testing
Test reporting
Config detection
Five ways to integrate code security into your workflow.
"Scan this repo for vulnerabilities and secrets."
Native integration for Claude Desktop and Cursor.
Type /codehardener to scan your project.
Full API for automation and CI/CD integration.
Block deploys that fail security policy checks.
No credit card required. All 30 scanners available on every plan.
For individual developers and side projects.
For developers shipping to production.
For teams with compliance requirements.
For organizations with advanced security needs.
"We went from zero security scanning to comprehensive coverage in an afternoon. 30 tools, one command. The SBOM generation alone saved us weeks of compliance work."
"Gitleaks caught hardcoded AWS keys in a PR that three human reviewers missed. Code Hardener paid for itself on day one."
"The MCP integration with Claude Code is seamless. Our developers scan their code without leaving their editor. Security adoption went from 20% to 95%."
Free tier includes 3 projects and 200 scans/month. No credit card required. See your first security findings in under 60 seconds.